It’s like a secret alleyway (say Diagon Alley from “Harry Potter”) in the sprawling city of the internet, known only to those who seek it out. As Director of Government Strategy at Authentic8, Abel advises the federal business team on policy development and budget trends to identify growth opportunities and shape customer engagement. Always document your actions, operate under an approved policy, and consult your legal counsel before engaging in activities that may involve criminal forums or marketplaces. Written rules of engagement and documented compliance protocols help teams stay within legal boundaries and demonstrate due diligence if their activity is ever reviewed or audited. A structured plan ensures all research aligns with organizational policy and legal guidelines. These simple pieces of advice can go a long way toward avoiding legal pushback, but as always, consult your legal and security departments to create an official policy.
Access To The Dark Web
The digital underworld known as the dark web remains a topic of intense curiosity and misunderstanding. Unlike the surface web indexed by search engines, this hidden portion of the internet requires specific tools, configurations, and knowledge to reach. Accessing the dark web is neither inherently illegal nor simple, yet it demands a deliberate departure from conventional browsing habits.
For credential monitoring, you need automated dark web monitoring that scans sources search engines can’t reach. The search engines themselves don’t pose risks, but the sites they index might. Enterprise security teams use automated dark web monitoring platforms instead of manual searching. Dark web sites use .onion domains that only resolve through the Tor network. What’s illegal is engaging in criminal activity on the dark web, like buying stolen data or illegal goods. These require automated monitoring that continuously watches sources search engines can’t reach.
- Think of it as a curated list of .onion links organized by category.
- Darknet, open web and deep web are three different concepts that describe different areas of the internet.
- Others can be reached with the right network settings or software, such as the Tor browser.
- The dark web is notorious for hosting a wide range of cyber threats that pose significant risks to individuals and organizations.
- It offers a free API that lets you integrate dark web searches into security tools and scripts.
- Because transactions are typically conducted using cryptocurrencies and encrypted communication channels, tracing these activities is notoriously difficult.
What Is Required for Entry?

Gaining access to the dark web typically begins with the Tor Browser, a modified version of Firefox that routes traffic through a global network of encrypted relays. This anonymizing technology masks the user’s IP address, but it is only the first step. Access to the dark web also involves navigating .onion domains—special addresses unreadable by standard browsers. Without this specialized software, the dark web remains completely invisible to ordinary internet users.
Legal and Practical Gateways
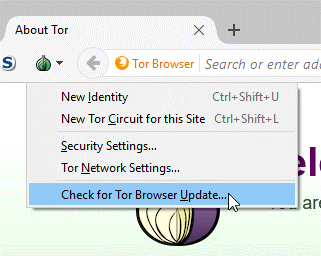
While access to the dark web is legal in most countries, the method of acquisition matters. Downloading Tor from its official website or a trusted repository ensures safety, whereas third-party sources may contain malware. Accessing the dark web also requires careful operational security: disabling JavaScript, avoiding plugins, and never entering personal information. Many users seek the dark web for privacy journalism, whistleblowing, or circumventing censorship, but the same pathways can expose users to illicit marketplaces or surveillance.
Navigating the Hidden Network
Once access to the dark web is established, the experience is starkly different from the surface web. Search engines like Ahmia or Haystak index a fraction of .onion sites, but most content is reached through word-of-mouth directories or link aggregators. Accessing the dark web often involves stumbling upon dead links or sites that vanish without warning. The lack of centralized regulation means that navigating this space demands constant vigilance and a clear purpose, whether for research, activism, or secure communication.
Risks and Misconceptions
Many believe access to the dark web automatically equates to criminal activity, but the reality is more nuanced. Accessing the dark web does provide a haven for illegal exchanges, yet it also hosts forums for political dissidents, encrypted email services, and privacy-focused libraries. The primary danger lies in the lack of accountability—scams, malware, and phishing are rampant. Users who venture into this realm must treat every click as potentially hostile, as the anonymity that protects them also shields malicious actors.
Maintaining Anonymity Beyond the Browser
Sustained access to the dark web requires more than just software. A virtual private network (VPN) layered before Tor can obscure the fact that you are using Tor at all. Access to the dark web also depends on strong operational security—using pseudonyms, never reusing passwords, and avoiding any action that could tie your online identity to your physical one. The foundation of safe access is understanding that the dark web is not a single destination but a diverse, fragile ecosystem where every decision can have lasting consequences.

