Their purpose is to give users a controlled and anonymous way to explore hidden services without exposing personal information or system details. This layered design makes it difficult for websites, internet providers, or outside observers to trace where a request originated. Users rely on Orbot with Tor Browser when they need secure mobile access to hidden sites or private communication. IOS users depend on Onion Browser when they need quick, private access without desktop tools. Tails routes all activity through secure channels and includes built-in anonymity tools. I2P began in 2003 as a project focused on creating a fully decentralized anonymity network separate from the public internet.
- Using dark web browsers like Tor is legal in most countries, but accessing illegal content or services remains unlawful regardless of the technology used.
- It is absolutely critical to know if your information is on the dark web in order to properly protect yourself from threats.
- This makes it possible for users to access the deep web without worrying about their browser history or behavior being monitored.
- If the result matches your real location, or if you see multiple IP addresses displayed, your VPN is not working properly and your anonymity is at risk.
- Cybersecurity pros watch these forums, too, to keep tabs on the cyberthreat landscape.
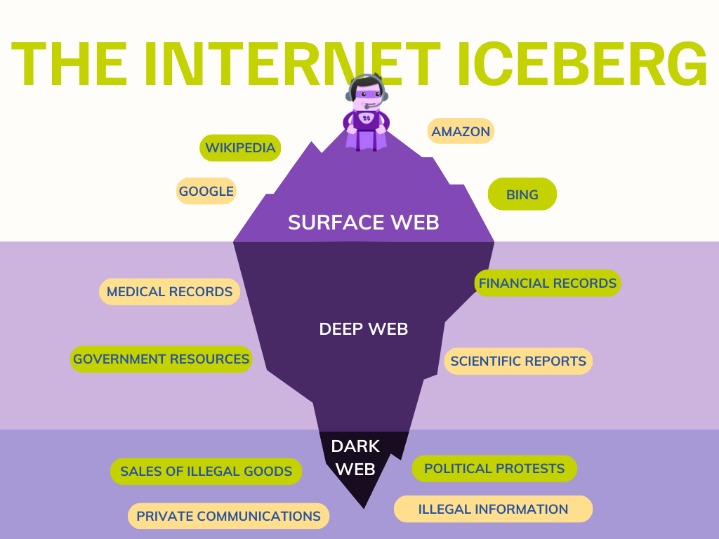
Here’s a closer look at the importance of protecting your online identity and implementing robust cybersecurity practices when accessing the dark web. In summary, while both the deep web and the dark web are parts of the internet not indexed by standard search engines, they serve hugely different purposes and populations. This includes any information that is protected behind paywalls, has restricted access, or is not linked to surface web pages in a way that search engines can easily discover.
Access The Dark Web
Venturing into the access the dark web landscape requires understanding that this hidden part of the internet is not indexed by standard search engines. Unlike the surface web, it relies on encrypted networks and specialized tools. While often associated with illicit activity, legitimate users also seek it for privacy, whistleblowing, or bypassing censorship. To navigate safely, you must follow strict protocols, as the environment is rife with scams and malicious actors.
Essential Tools for Accessing the Dark Web
To begin, you cannot simply open a standard browser. Access the dark web typically demands the Tor Browser, which routes your traffic through multiple layers of encryption. Other methods include the I2P network or VPNs, though Tor remains the most common. Below are the critical components:
- Tor Browser – Download only from the official project website to avoid trojans.
- VPN (Virtual Private Network) – Use one for an added layer of anonymity before launching Tor.
- Secure Operating System – Consider Tails or Whonix, which run from USB drives and leave no traces.
- Cryptocurrency – Bitcoin or Monero for any transactions, as credit cards are unsafe.
Step-by-Step Process to Access the Dark Web
Following a structured approach reduces risks. Remember that access the dark web without preparation can expose your IP address. Here is a numbered guide:
- For instance, journalists might use DarkWebLinks to find established forums where hackers hang out, as opposed to discovering a fake forum via search that’s actually a phishing trap.
- It is also known as the black web and underground internet.
- Business operations requiring confidentiality, credential-protected services, internal corporate systems, and regulatory compliance with data protection requirements
- Additional steps depend on what type of Deep Web content you’re looking for.
- That said, the social network’s data collection and tracking practices may seem at odds with many of the principles motivating dark web users.
- Install a VPN – Choose a no-logs provider and connect to a server in a privacy-friendly jurisdiction.
- Download Tor Browser – Verify the file’s signature with GPG to ensure authenticity.
- Disable Scripts – In the browser’s security settings, set it to “Safest” to block JavaScript.
- Navigate Carefully – Use .onion directories like The Hidden Wiki but avoid clicking random links.
- Exit Properly – Close all tabs and clear cache after each session.
Common Risks and Safety Measures
Access the dark web exposes users to malware, phishing sites, and surveillance. Even well-intentioned explorers can stumble into illegal content. Always disable plugins, avoid downloading files, and never share personal information. Law enforcement actively monitors the network, so use pseudonyms and burnable email addresses.
FAQs
Q: Is it illegal to access the dark web?
A: No, access the dark web itself is legal in most countries. However, viewing or distributing illegal content (e.g., child abuse, stolen data) is a crime.
Q: Can my ISP see that I am accessing the dark web?
A: Yes, your ISP can detect Tor usage, but not your destination. Using a VPN hides this from your ISP.
Q: What is the safest way to access the dark web?
A: Combine a VPN, Tor Browser in “Safest” mode, and run the browser from a live OS like Tails. Avoid logging into personal accounts.
Recommended .onion Resources (for research only)
- DuckDuckGo’s onion service – A search engine that doesn’t track you.
- SecureDrop – Used by journalists for anonymous tips.
- ProtonMail – Encrypted email service with an onion address.
- The Tor Project’s official site – For updates and safety guides.
Final note: Access the dark web responsibly. The anonymity it provides comes with ethical and legal responsibilities. Always prioritize cybersecurity and respect the law.