Access Dark Web
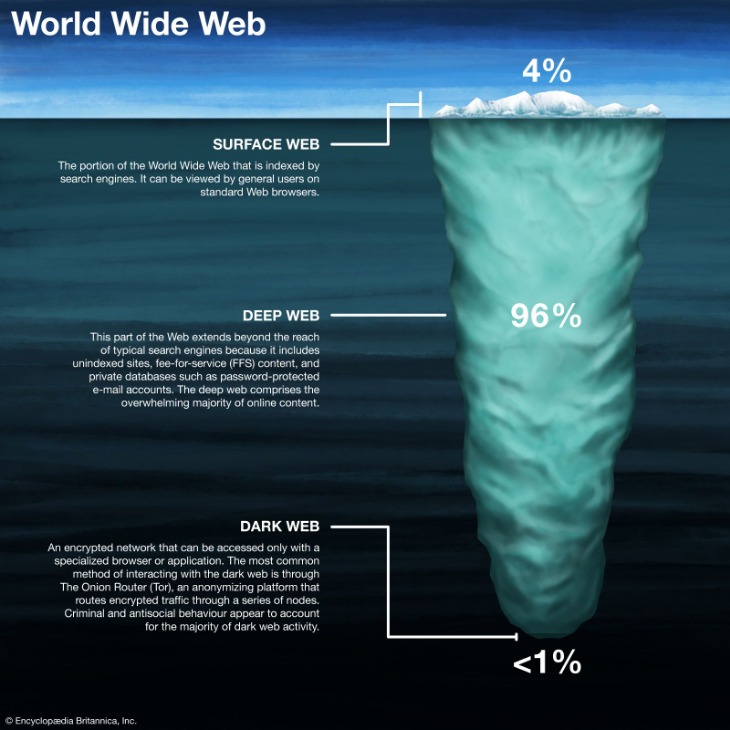
The digital realm known as the dark web is a hidden segment of the internet not indexed by standard search engines. Unlike the surface web you use daily, accessing it requires specialized software, configurations, or authorization. This layered network, while often associated with illicit activities, also serves as a vital tool for privacy advocates, journalists, and citizens in repressive regimes. To access the dark web, users must first understand its infrastructure and the tools that unlock its encrypted corridors.
- If the crawler can’t access a webpage to index its contents, the webpage does not “surface” and thus remains unindexed—this is the Deep Web.
- Be cautious about the links you click on, as not all content is safe or legal.
- The Tor browser can also access regular web content while strengthening user anonymity.
- Lastly, there's the dark web, a concealed part of the deep web known for its high anonymity.
A second-pass research flow benefits most, especially after core entities and terms are already identified. It is often used when researchers want structured exploration instead of purely keyword-ranked results. That model supports brand monitoring, leak keyword tracking, and other repeatable threat-intelligence tasks. Instead of being browsing-first, it emphasizes programmatic querying and repeatable tracking. DarkSearch became publicly visible by 2019 and stands out for treating dark web discovery as a monitoring problem.
- Multiple sites maintain frequently-updated lists of suspicious IP addresses that are known for illicit or malicious content.
- These are sites that require login or subscription services to access, such as academic journals, court record databases, or even services like Netflix.
- To keep your online activities private, the Dark Web uses advanced encryption, different from what you use every day.
- Additional features like market and forum search capabilities, API access, and regularly updated directories enhance the safety and efficiency of navigating the dark web.
- And all the Dark Web sites have weird domain addresses and end in .onion suffix so that they are much harder to track and only accessible by Tor.
For example, it’s dangerous to buy or download anything from illegal marketplaces — the downloaded files may contain malware and the police can trace illegal purchases. The dark web is so named because of its hidden configurations, its emphasis on anonymity, and the private activity that happens there. It’s notorious for illegal activity, but many people use it just to browse anonymously. "Understand that the web as we know it today is privacy-hostile and that nothing is foolproof, do research, support organisations and projects — like Tor Project, i2p, and Open Privacy — that are building and maintaining tools that make enforcing your consent easier."
Essential Tools for Dark Web Entry
The most common method to access the dark web is through the Tor Browser, which routes your traffic through multiple relays to anonymize your location. Downloading it from the official website is the first step. After installation, accessing dark web sites—those ending in .onion—becomes possible directly within the browser. Another alternative is the I2P network, which creates a separate, encrypted layer for peer-to-peer communication. Whichever tool you choose, remember that simply wanting to access the dark web does not automatically grant safety; caution is paramount.
Navigating Risks and Protocols
When you access the dark web, your digital footprint is reduced but not erased. ISPs can still see you are using Tor, and malicious exit nodes may monitor unencrypted traffic. To mitigate these risks, access the dark web only with a dedicated device or a secure virtual machine. Never share personal information, and disable JavaScript in the Tor Browser settings for heightened security. The phrase "access the dark web" often conjures danger, but with rigorous operational security, it becomes a controlled environment for exploring censored content or communicating anonymously.
Common Entry Points and Directories
Finding sites once you access the dark web is challenging without directories. Resources like The Hidden Wiki or Dark.fail provide curated lists of verified .onion links. To access the dark web effectively, bookmark a few reliable directories before diving deeper. Always verify URLs multiple times to avoid phishing clones. When you access the dark web through these indexes, focus on forums for cryptography, privacy tools, or news aggregators rather than unmoderated marketplaces, which are frequently monitored by law enforcement.

Legal and Ethical Boundaries
It is not illegal to access the dark web in most jurisdictions; the legality depends on your actions while there. Downloading pirated materials, purchasing illegal substances, or accessing contraband carries severe penalties. To responsibly access the dark web, stick to ethical uses like protecting whistleblower communications or reading banned literature. The act itself—using Tor to access the dark web—is a neutral technical step, but the content you consume defines your legal exposure. Always operate within local laws and ethical standards.