Acess The Dark Web
The dark web represents a hidden layer of the internet, intentionally concealed from standard search engines and accessible only through specialized software like Tor. While often associated with illicit activity, it also hosts legitimate uses such as anonymous communication, privacy protection, and access to censored information. Access the dark web requires careful preparation to avoid security threats and legal pitfalls. This article provides a practical guide for access the dark web safely, covering tools, risks, and best practices.
Instead, you have to use specific tools and processes. Some of them (the hardest ones to access) are situated in what is known as the dark web. Their efforts help to identify, mitigate, and prevent a wide range of cyber-attacks, ultimately enhancing the overall cybersecurity posture of the organizations they serve.
What Is the Dark Web?
The dark web is part of the deep web—content not indexed by search engines. Unlike the surface web, it relies on encrypted networks like Tor (The Onion Router) or I2P. Access the dark web means using these networks to reach .onion sites, which are not accessible with standard browsers.
Essential Tools for Access the Dark Web
- Tor Browser: The most common tool. Download only from the official Tor Project website to avoid malware.
- VPN (Virtual Private Network): Adds an extra layer of encryption. Use a no-log VPN before launching Tor for access the dark web.
- TAILS OS: A live operating system that routes all traffic through Tor, leaving no traces on your computer.
- Secure email providers: Services like ProtonMail (also accessible via .onion) for anonymous communication.
Step-by-Step Guide to Acess The Dark Web
- Prepare your system: Update your OS, disable JavaScript in Tor Browser (via security settings), and avoid torrenting over Tor.
- Install a VPN: Connect to a VPN server in a jurisdiction with strong privacy laws. This hides Tor usage from your ISP.
- Download Tor Browser: Verify the file’s signature (GPG) to ensure integrity. Do not use third-party mirrors.
- Launch Tor Browser and wait for the connection test. Acess the dark web by typing .onion URLs into the address bar.
- Use directories cautiously: Start with reputable directories like The Hidden Wiki (verify links via community forums).
Risks and Safety Measures
While access the dark web offers anonymity, it carries significant risks:
- Malware: Many sites host malicious scripts. Keep Tor Browser’s security level at “Safest” (disables JavaScript).
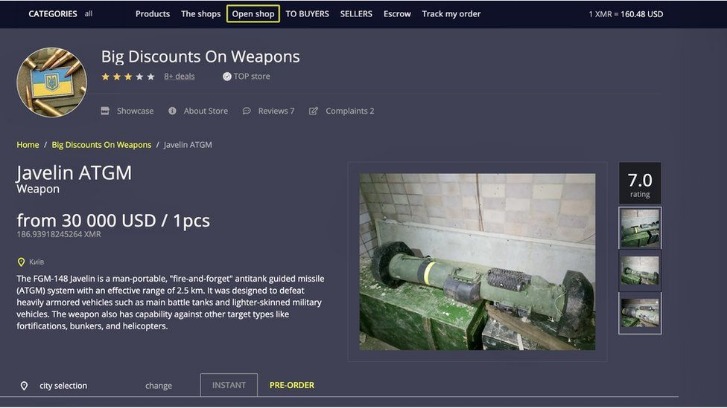
- Scams: Avoid marketplaces requiring cryptocurrency payments; use escrow services only from trusted sources.
- Legal dangers: Accessing illegal content (e.g., weapons, child abuse) is criminal. Stick to forums, privacy tools, and research.
- Surveillance: Law enforcement monitors .onion sites. Never provide personal information or use real login credentials.
FAQs About Acess The Dark Web
- As explained earlier, you won’t be able to access the dark web the same way you would the surface web.
- Malware, ransomware, and hacking tools are also readily available for purchase or rent, enabling attackers to launch sophisticated campaigns.
- DuckDuckGo’s onion service is best for general use and privacy though it’s not dark web specific.
- It was created for people who want occasional anonymity without using a separate browser.
Is it illegal to access the dark web?
No, using Tor is legal in most countries. However, engaging in illegal activities (e.g., buying stolen data) is not. Always verify local laws before access the dark web.
Can I get malware from acess the dark web?
Yes. Always use a sandboxed environment or a dedicated device. Never download files or click unknown links.
How do I find reliable .onion sites?
Use Darknet Live or The Hidden Wiki (via authenticated mirrors). Cross-reference links on privacy-focused subreddits (e.g., r/onions).
What is the difference between dark web and deep web?
The deep web includes all non-indexed content (e.g., private databases, email accounts). The dark web is a small, encrypted subset requiring specific tools for access the dark web.
Final Considerations
For robust anonymity, combine a VPN, Tor Browser, and a secure OS. Acess the dark web only for legitimate purposes—privacy advocacy, research, or bypassing censorship. Never ignore warnings about phishing sites or fake identity verification pages. Treat every .onion domain with skepticism until verified through multiple independent sources.