Accessing The Dark Web
- While the Tor browser works like a standard browser, web addresses on the dark web tend to be a mix of random numbers and letters, making it difficult for users to find the requisite information.
- He has expertise in cyber threat intelligence, security analytics, security management and advanced threat protection.
- Users can also access research papers for free that are submitted by the original authors.
- This makes it a powerful tool for tracking infrastructure or investigating network relationships between hidden services.
Understanding these threats is crucial for anyone venturing into the dark web, as it prepares them to take proactive measures for dark web protection and to safeguard their digital assets. Navigating the dark web comes with inherent risks due to its anonymity and lack of regulation. Understanding these distinctions is crucial for employing robust dark web protection and security.
Tor shares similarities with VPNs and proxy servers — all of these tools allow anonymous browsing. On Tor, you can type in any URL you’d like to visit, including .onion links on the dark web. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. One of the challenges of exploring the dark web is that you can’t just use a search engine and type in what you’re after like you would on the surface web.
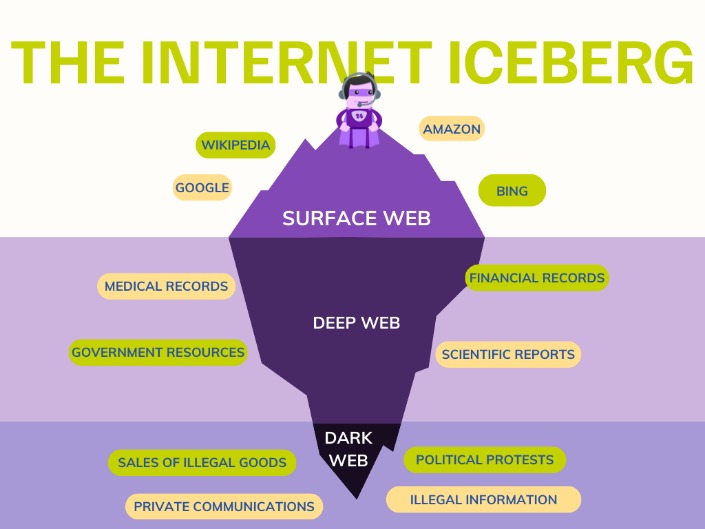
The dark web represents a small, encrypted portion of the internet not indexed by standard search engines like Google or Bing. Unlike the surface web you use daily, accessing the dark web requires specialized software, configurations, and an understanding of its unique risks and purposes. This article provides a factual overview of the methods and considerations involved in accessing the dark web, focusing on technical steps and legal boundaries.
- Remember, the more layers of security you have, the safer your experience will be.
- Open programs can log, sync, or share information in the background, reveal your real IP address, or create data traces that undermine your anonymity.
- To navigate the dark web safely and maintain anonymity, certain tools and methods are necessary.
- Maintain a complete record of activities while on the dark web and have a policy in place for “rules of engagement” when on sites where criminal activity may occur.
- Using the wrong browser exposes you to risks that hidden services often exploit to identify or target visitors.
- Tor stands for "The Onion Router," with the onion serving as a reference for the different layers of the internet.
What You Need for Accessing The Dark Web
To begin accessing the dark web, you must download and install the Tor Browser. This is the most common gateway, routing your traffic through multiple encrypted relays to anonymize your location. Another option is I2P, which creates its own network layer for accessing the dark web, though it is less user-friendly. Both tools are free and open-source, but accessing the dark web without proper precautions can expose you to malware or surveillance. Always verify the authenticity of the software from official sources.
Step-by-Step Process for Accessing The Dark Web
After installing the Tor Browser, accessing the dark web involves typing a .onion address into the URL bar. These addresses are only reachable through Tor. For example, a common starting point is the Hidden Wiki, a directory of onion sites. However, accessing the dark web this way does not guarantee safety; avoid clicking on unknown links, as many lead to scams or illegal content. Using a VPN before accessing the dark web adds an extra layer of anonymity by encrypting your traffic to the Tor entry node.
Risks and Precautions When Accessing The Dark Web
While accessing the dark web can be legal for privacy reasons, it is also a haven for illicit activities. Law enforcement actively monitors dark web marketplaces and forums. To protect yourself, disable JavaScript on the Tor Browser to prevent exploits. Accessing the dark web without a strict separation from your personal data is risky; never use real names, emails, or financial accounts. A dedicated virtual machine or live USB can isolate accessing the dark web from your main system.
Common Uses for Accessing The Dark Web
Many journalists and activists rely on accessing the dark web for secure communication in oppressive regimes. Whistleblowing platforms, such as SecureDrop, use .onion services for anonymous submissions. Additionally, accessing the dark web allows users to bypass censorship and access information banned in their country. However, the same infrastructure supports illegal markets, which is why authorities emphasize that accessing the dark web requires personal responsibility and knowledge of local laws.

Final Technical Notes on Accessing The Dark Web
For reliable accessing the dark web, ensure your system is updated and free of malware. Using a search engine like DuckDuckGo’s onion service can help find legitimate sites. Remember that speed on the dark web is significantly slower due to routing through multiple relays. Accessing the dark web is not inherently illegal, but engaging with illegal content is. Always prioritize digital hygiene and ethical use when accessing the dark web.